secure symmetric authentication for rfid tags In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of .
0 · Secure symmetric authentication for RFID tags
1 · Secure Symmetric Authentication for RFID Tags
NFC works on top of three crucial innovations in wireless tag readers, cryptographic credit card .
Secure symmetric authentication for RFID tags
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric .
smart card expo noida
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.This work employs a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID tag, and proposes an authentication mechanism to overcome current vulnerabilities.
Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al. To address the issues mentioned above, we propose an Efficient, Secure, and practical ultra-lightweight RFID Authentication Scheme (ESRAS), which uses rank operation for low-cost tags. We utilize a simplistic bitwise exclusive-OR, circular left rotation, and a newly proposed ultra-lightweight rank operation to provide high security at low cost.
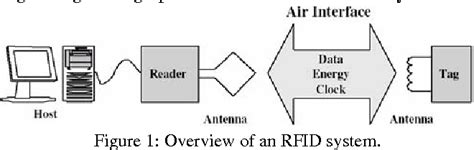
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research projectThe three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Starting with a short introduction into common RFID systems along with passive tags, we have a tendency to gift a motivation why secure authentication with standardized parallel crypto algorithms for RFID tags is foremost for some applications.The project ART proposes to reinforce passive RFID (Radio Frequency Identification) tags with cryptographically secure authentication. beginning with a brief introduction into common RFID systems with passive tags, we have a tendency to gift a motivation why secure authentication with standardized parallel crypto algorithms for RFID tags is .In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.
This work employs a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID tag, and proposes an authentication mechanism to overcome current vulnerabilities. Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al. To address the issues mentioned above, we propose an Efficient, Secure, and practical ultra-lightweight RFID Authentication Scheme (ESRAS), which uses rank operation for low-cost tags. We utilize a simplistic bitwise exclusive-OR, circular left rotation, and a newly proposed ultra-lightweight rank operation to provide high security at low cost.Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research projectThe three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems. Starting with a short introduction into common RFID systems along with passive tags, we have a tendency to gift a motivation why secure authentication with standardized parallel crypto algorithms for RFID tags is foremost for some applications.
Secure Symmetric Authentication for RFID Tags
smart card failure in sun direct means

The hub for all your updates on My Nintendo. Earn points by playing apps on your smart .Ensure that wireless communication is enabled on your system. Press the POWER button on the NFC Reader. The power LED will turn on blue. If the battery power is getting low the LED will turn red. Place the Nintendo 3DS NFC Reader/Writer and the handheld system on a flat level .
secure symmetric authentication for rfid tags|Secure Symmetric Authentication for RFID Tags