some smart cards use telescopic data in the card For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction. 8 PCS Metroid Dread Mini NFC Cards Including Metroid: Samus Returns, .
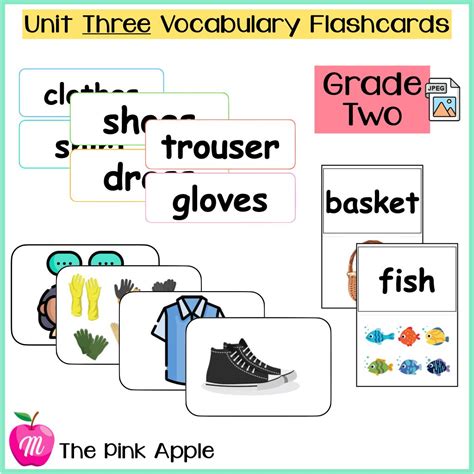
0 · unit 3 Flashcards
1 · Smart Cards vs. Proximity Cards
2 · How does a smart card work?
3 · Chapter 3: Storage Flashcards
4 · Ch3 Test Flashcards
Specifications. Tap And Rate! ⭐. Zappycards uses the latest NFC technology, used in Apple Pay and Google Pay, to make reviews happen with just a tap of your phone. It's like magic to get reviews! Step 1: Simply tap the phone on the .
For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.For an extra level of security, some smart cards today store ____ data in the card .For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.
For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction. Successful attacks against smart cards have included power glitching; differential power analysis; and capping them then using an ion-beam microscope to read out the key bits from the flash memory. Because the cards are always at risk of being stolen by an advanced attacker, each card is usually issued a unique key. Some people confuse smart cards with prox cards because both use radio waves as a part of their systems. However, this does not mean they can be used interchangeably, and there are evident differences between the two access control card technologies.
Smart cards greatly improve the convenience and security of any transaction. They provide tamper-proof storage of user and account identity. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. Smart card systems have proven to be more reliable than other machine-readable cards, like magnetic strips and barcodes. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network.
unit 3 Flashcards
Smart cards are credit or debit cards that contain an embedded microprocessor chip. These microprocessors are able to store and process data directly. Unlike traditional magnetic stripe cards, they don’t require a remote connection.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.With an embedded microcontroller, smart cards have the unique ability to store large amounts of data, carry out their own on-card functions (e.g., data storage and management, encryption, decryption, and digital signature calculations) and interact intelligently with a smart card reader.For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.
For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.For an extra level of security, some smart cards today store ____ data in the card and use that data to authenticate the card's user before authorizing the smart card transaction.
Successful attacks against smart cards have included power glitching; differential power analysis; and capping them then using an ion-beam microscope to read out the key bits from the flash memory. Because the cards are always at risk of being stolen by an advanced attacker, each card is usually issued a unique key. Some people confuse smart cards with prox cards because both use radio waves as a part of their systems. However, this does not mean they can be used interchangeably, and there are evident differences between the two access control card technologies.Smart cards greatly improve the convenience and security of any transaction. They provide tamper-proof storage of user and account identity. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network.
Smart card systems have proven to be more reliable than other machine-readable cards, like magnetic strips and barcodes. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network.Smart cards are credit or debit cards that contain an embedded microprocessor chip. These microprocessors are able to store and process data directly. Unlike traditional magnetic stripe cards, they don’t require a remote connection.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
Smart Cards vs. Proximity Cards

How does a smart card work?
Chapter 3: Storage Flashcards
500 million. The reach of HiHello digital business cards, email signatures, and virtual backgrounds in the past year. Share your card with anyone using its QR, text message, email, link, WhatsApp, social media, Apple Watch, Apple .Our customer support is available Saturday to Thursday: 11am-5:30pm. Average answer time: .
some smart cards use telescopic data in the card|Chapter 3: Storage Flashcards