rfid tag access control RFID access control refers to systems that use RFID technology to allow or deny access to a particular area or facility. The system uses RFID key cards or tags, which carry embedded microchips that communicate wirelessly with RFID readers installed at multiple access points, such as doors or gates, to manage access. This means your iPhone 12 Pro is good to go. Hope someone else can confirm. I can confirm .
0 · rfid gate access control systems
1 · rfid based door access control
2 · rfid access control wiring diagram
3 · rfid access control system price
4 · rfid access control system pdf
5 · rfid access control manual pdf
6 · rfid access control manual
7 · rfid access control instructions
Here’s how you can access the NFC Tag Reader on your iPhone and use it not just for the payments but also for so may other things and automate a lot of tasks.Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put your iPhone near the NFC tag. Enter a name for your tag. .
A complete RFID access control system typically consists of three main components: RFID tags, readers and writers, and management software. Users attach RFID tags as identification devices, while readers and writers send and receive signals to read tag information. RFID access control refers to systems that use RFID technology to allow or deny access to a particular area or facility. The system uses RFID key cards or tags, which carry .
A complete RFID access control system typically consists of three main components: RFID tags, readers and writers, and management software. Users attach RFID tags as identification devices, while readers and writers send and receive signals to read tag information.
rfid 125khz read write
RFID access control refers to systems that use RFID technology to allow or deny access to a particular area or facility. The system uses RFID key cards or tags, which carry embedded microchips that communicate wirelessly with RFID readers installed at multiple access points, such as doors or gates, to manage access.RFID access control uses a system of tags, readers, and computer servers to allow access to verified users. The pros of RFID entry systems are ease of use, easy replacement, and practicality for doors, gates, vehicles, and elevators. An RFID access control system consists of four main components: RFID tags: These are typically embedded in key cards or key fobs and contain unique identifying information. Antennas: They receive signals from the RFID tags and transmit them to the RFID reader. Access can be precisely managed and monitored by equipping doors and entry points with RFID readers and issuing RFID tags, key cards, or mobile devices with embedded RFID chips to authorized individuals.
RFID tags consist of three key elements: a microchip, antenna and a substrate. The microchip within the tag is what stores and processes information, modulates and demodulates radio-frequency signals. And antenna enables the tag to receive and transmit the signal. RFID tags can be differentiated by their power supply.
rfid gate access control systems
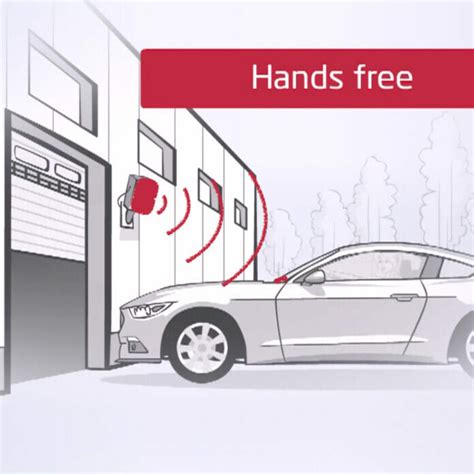
RFID access control systems work by utilizing a series of tags, readers and computer servers to grant door access to any authorized individuals in possession of valid credentials. RFID access control uses a system of tags, readers, and computer servers to allow access to verified users. The pros of RFID entry systems are ease of use, easy replacement, and practicality for doors, gates, vehicles, and elevators.
RFID access control system allows determines who enters or leaves specific premises at any given time. It includes an automated system that identifies an individual, authenticates their details, and allows access upon verification. The system is designed to only allow specific individuals to access a building. RFID access control, then, is a system that uses electromagnetic radio frequencies to transmit crucial identifying data from tags on access control credentials to door readers so that they may be assessed by the system for access decision-making.
A complete RFID access control system typically consists of three main components: RFID tags, readers and writers, and management software. Users attach RFID tags as identification devices, while readers and writers send and receive signals to read tag information.
RFID access control refers to systems that use RFID technology to allow or deny access to a particular area or facility. The system uses RFID key cards or tags, which carry embedded microchips that communicate wirelessly with RFID readers installed at multiple access points, such as doors or gates, to manage access.RFID access control uses a system of tags, readers, and computer servers to allow access to verified users. The pros of RFID entry systems are ease of use, easy replacement, and practicality for doors, gates, vehicles, and elevators.
An RFID access control system consists of four main components: RFID tags: These are typically embedded in key cards or key fobs and contain unique identifying information. Antennas: They receive signals from the RFID tags and transmit them to the RFID reader.
Access can be precisely managed and monitored by equipping doors and entry points with RFID readers and issuing RFID tags, key cards, or mobile devices with embedded RFID chips to authorized individuals. RFID tags consist of three key elements: a microchip, antenna and a substrate. The microchip within the tag is what stores and processes information, modulates and demodulates radio-frequency signals. And antenna enables the tag to receive and transmit the signal. RFID tags can be differentiated by their power supply.RFID access control systems work by utilizing a series of tags, readers and computer servers to grant door access to any authorized individuals in possession of valid credentials.
RFID access control uses a system of tags, readers, and computer servers to allow access to verified users. The pros of RFID entry systems are ease of use, easy replacement, and practicality for doors, gates, vehicles, and elevators. RFID access control system allows determines who enters or leaves specific premises at any given time. It includes an automated system that identifies an individual, authenticates their details, and allows access upon verification. The system is designed to only allow specific individuals to access a building.
rfid active blocker card

rfid based door access control
rfid access control wiring diagram

rfid alarm card
rfid access control system price
No, you do not need an NFC card to use amiibo. However, you will need a .I have the N2 Elite which comes with the N2 Elite disc and its micro-USB reader/writer. Is there a software application that allows me to use only the micro-USB reader/writer with blank Ntag215 NFC chips? I feel like this should be possible but I tried with one piece of software (wakdev .
rfid tag access control|rfid access control manual pdf