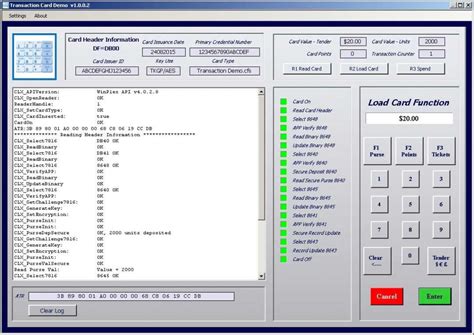
secure memory smart card software M.O.S.T. Toolz™ II enables programmers to create a smart card-based transaction system that updates and secures files while setting a variety of defensive measures to protect user ID, card access, and file information. Mobile-based access control relies on a couple of different technologies: RFID and Bluetooth. Specifically, many phones use the NFC standard of RFID and the BLE standard of Bluetooth for such unlocks. Both work without needing to pair .NFC tags can be used to automate tasks and improve daily routines, such as connecting to Wi-Fi or Bluetooth networks, managing sleep .Nfc security. NFC makes quick, contactless payments possible, but it comes with security risks like eavesdropping, relay attacks, and malware. Understanding these threats helps businesses and users stay protected. .
0 · Smart Card Authentication
1 · M.O.S.T. Toolz™ II SDK – Contact + Contactless Smart Cards
Mobile-based access control relies on a couple of different technologies: RFID and Bluetooth. Specifically, many phones use the NFC standard of RFID and the BLE standard of Bluetooth for such unlocks. Both work without needing to pair .
M.O.S.T. Toolz™ II enables programmers to create a smart card-based .

Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a .Smart cards come in two varieties: memory and microprocessor (smart chip). Memory cards store data and can be viewed as small USB memory sticks with optional security. On the other hand, a microprocessor card can add, delete, and manipulate information in its memory on the card.M.O.S.T. Toolz™ II enables programmers to create a smart card-based transaction system that updates and secures files while setting a variety of defensive measures to protect user ID, card access, and file information.Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a traditional credit card form factor, enabling organizations to address their PKI security needs.
CardLogix offers an extensive portfolio of in-house smart card programming services from simple scripts for I2C non-volatile memory to Java applets and custom card operating systems.CardLogix manufacturers a wide range of secure protected memory and CryptoMemory smart cards by Atmel, EM Systems and Infineon.
Our Best-in-Class Managed PKI now comes with Smart Card configuration and management technology. Everything you need to configure PIV-Backed Smart Cards for Desktop Logon, Wi-Fi, SSH, VPN, Application Authentication, and much more. Memory cards control how their memory is written to and read from, Microprocessor cards run approved applications that have been coded in a secure manner as to prevent outside applications from accessing their memory space.
Release Notes. View SD and microSD card information & S.M.A.R.T. analysis. Maintain optimal performance by reviewing SD and microSD card information and S.M.A.R.T. analysis. Monitor SD and microSD card usage status. Track the wear level of Transcend SD and microSD memory cards. New cards display a value of 100%, which decreases with use.
Memory Card Configuration Software for: I²C Straight Memory Cards. Protected Memory Cards. Superior Data Security with Card Configuration Utility™ Software. Robust, I²C Memory Card Demonstration Software with Templates. Includes 14 Atmel and Microchip Chip Cards, Readers, and Software. Add to Cart. Add to wishlist. Smart card developers and marketing experts have many choices of smart card system design, including: Multi-application smart cards; Single-application programmable chipcards; Smart cards with a fixed set of functions; Secure memory cardsSmart cards come in two varieties: memory and microprocessor (smart chip). Memory cards store data and can be viewed as small USB memory sticks with optional security. On the other hand, a microprocessor card can add, delete, and manipulate information in its memory on the card.
M.O.S.T. Toolz™ II enables programmers to create a smart card-based transaction system that updates and secures files while setting a variety of defensive measures to protect user ID, card access, and file information.Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a traditional credit card form factor, enabling organizations to address their PKI security needs.CardLogix offers an extensive portfolio of in-house smart card programming services from simple scripts for I2C non-volatile memory to Java applets and custom card operating systems.CardLogix manufacturers a wide range of secure protected memory and CryptoMemory smart cards by Atmel, EM Systems and Infineon.
Our Best-in-Class Managed PKI now comes with Smart Card configuration and management technology. Everything you need to configure PIV-Backed Smart Cards for Desktop Logon, Wi-Fi, SSH, VPN, Application Authentication, and much more. Memory cards control how their memory is written to and read from, Microprocessor cards run approved applications that have been coded in a secure manner as to prevent outside applications from accessing their memory space.Release Notes. View SD and microSD card information & S.M.A.R.T. analysis. Maintain optimal performance by reviewing SD and microSD card information and S.M.A.R.T. analysis. Monitor SD and microSD card usage status. Track the wear level of Transcend SD and microSD memory cards. New cards display a value of 100%, which decreases with use.Memory Card Configuration Software for: I²C Straight Memory Cards. Protected Memory Cards. Superior Data Security with Card Configuration Utility™ Software. Robust, I²C Memory Card Demonstration Software with Templates. Includes 14 Atmel and Microchip Chip Cards, Readers, and Software. Add to Cart. Add to wishlist.
Smart Card Authentication
rfid based library management system in india
Nfc-frog supports multiple modes for reading card data. See more
secure memory smart card software|Smart Card Authentication